Minimal viable protocol
With these issues in mind we can construct a minimally viable protocol for creating and publishing pairwise comparisons in a decentralized context.
Desired features
Our desired features for such a protocol include:
- Calculating pairwise comparisons between nodes so we can tell whether their work results were within an acceptable error threshold for a given task.
- Publishing and sharing data on some medium M—for example a blockchain like Ethereum or a decentralized communications platform like XMTP.
- A way to stop each node from prematurely stealing another node’s work.
- A way to stop nodes from lying about their side of a pairwise comparison.
- Surfacing disputes wherever the protocol makes that possible.
- Identifying the minimally required stakeholders in the protocol.
- A defined threshold for acceptable errors.
Specification
The generalized CRPC protocol lets multiple nodes independently verify each other’s work through these steps:
- Distribute the work to all nodes.
- Nodes independently perform their work.
- Generate commitments for the work results.
- Publish commitments for the work results.
- Reveal the original work and the salts used to build those commitments.
- Compute distances between results as pairwise comparisons.
- Generate commitments for the pairwise comparisons.
- Publish commitments for the pairwise comparisons.
- Reveal the pairwise comparisons and their salts.
- The originator reviews the outcome and decides whether the pairwise comparisons are acceptable.
The protocol uses two commit–reveal rounds: the first stops nodes from free-riding on others’ work after seeing it; the second stops them from lying about pairwise comparisons. That structure supports decentralization and creates several natural dispute surfaces.
Let n be the number of nodes in a graph N with . Let be the nodes in the run. Each node holds salts and —one pair per commit–reveal round—usable as disposable randomness for commitments.
Coordination happens over a medium M (blockchain, messaging layer, etc.).
All nodes are assumed to share a known function f used to execute the work W.
Formal step summary (KaTeX)
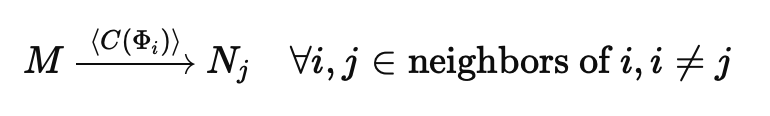
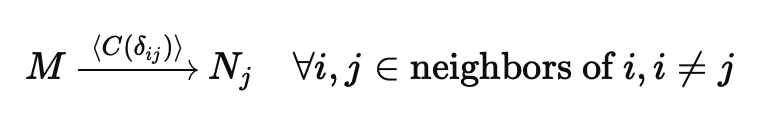
Let M be the medium (broadcast to all parties where needed). Salts , bind the two commit–reveal rounds.
Protocol detailed steps
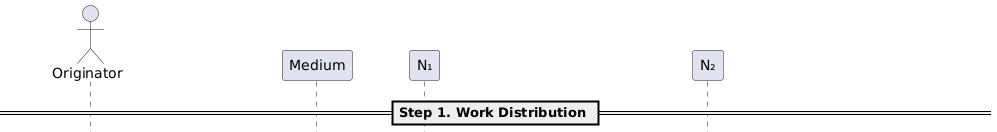
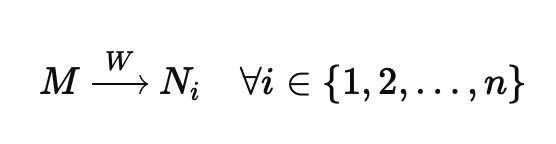
Step 1: Work distribution
The originator O selects (by whatever policy you use) which nodes may service W, then distributes W over M to every node in N.
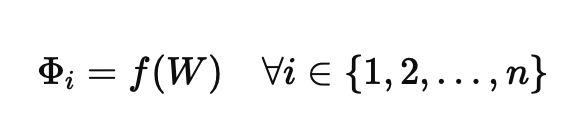
Step 2: Independent work execution
Each runs f on W independently. Outputs may be non-deterministic or noisy; node i’s result is .
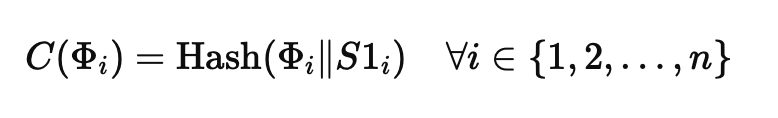
Step 3: Work commitments created
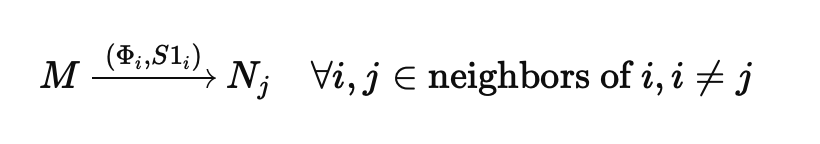
Each forms a hash-based commitment to together with salt .
Step 4: Work commitments published
Each node publishes its work commitment on M. Everyone sees an immutable promise of what will be opened next—no post-hoc edits to after others have committed.
That removes a wait-and-see strategy: commitments are public before reveals, so a node cannot quietly copy another’s labor and claim it as its own.
Dispute point 1 — timeouts: The first moment disputes can appear is a timeout: an implementation must define how to treat nodes that fail to publish work commitments on M in time.
Step 5: Work revealed
Each node publishes and so neighbors can check and proceed to distance / comparison work.
Note: Heavy payloads can live on L2 or blobs while M carries commitments and pointers—useful if the originator or others need material when a dispute opens at this stage.
Dispute point 2 — timeouts and commitment checks: Timeouts apply again. After reveal, any node can recompute a neighbor’s commitment; mismatches are evidence that a node lied about its work.
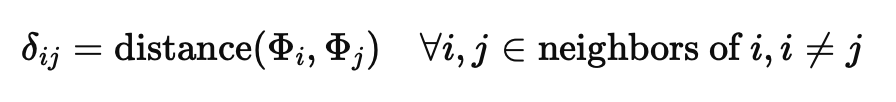
Step 6: Distance calculations as pairwise comparisons
With visible to neighbors , each edge uses a distance appropriate to f (e.g. SSIM for images, embedding distance for text).
For every reference comparison , we assume two reciprocal measurements: i → j and j → i. Each node publishes the comparison it computed toward each neighbor.
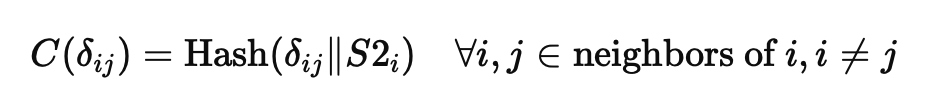
Step 7: Pairwise comparison commitments created
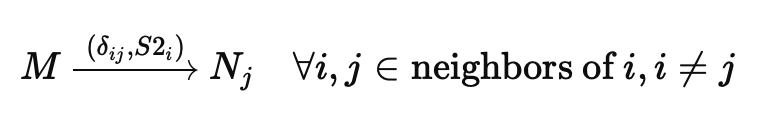
Each commits to its reported toward each neighbor , using salt .
Step 8: Pairwise comparison commitments published
Nodes publish on M, mirroring the work-commitment phase: they cannot rewrite comparisons after seeing neighbors’ values, and cannot steal a neighbor’s comparison claim.
Dispute point 3 — timeouts: As with dispute point 1, some nodes may fail to publish comparison commitments in time.
Note: These commitments are small; they can sit on-chain if M is a chain.
Step 9: Pairwise comparisons revealed
Each node publishes and so can be verified.
Dispute point 4 — reciprocal mismatch: On each edge, nodes can dispute if their reciprocal calculations do not match—i.e. the edge that should realize is inconsistent with and .
Note: Scalar values can also be stored on-chain for contracts to validate and to drive automation in the final step.
Step 10: Verification
O uses the stored pairwise comparisons: compare to , flag disputes, and run any decision logic that depends on acceptable comparisons.
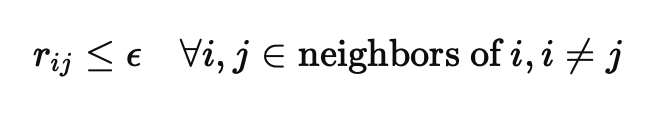
By this step, reciprocal disagreements are expected to have been surfaced in step 9. Acceptability can be checked once per edge using the mutual reference value with
(under the “similar enough” reading of the threshold; other tasks may invert the inequality as in the randomness example.)
At this point the run has let many nodes publish pairwise comparisons decentralized, while mitigating theft of work and blatant lying about comparisons.
Sequence diagram for two nodes
Below is the conceptual sequence for two nodes over an abstract medium M, emphasizing where disputes can arise and what kind they are. The appendix keeps PlantUML source for tooling; this page renders the same flow with Mermaid (Nextra compiles fenced mermaid code blocks automatically).